The modern was of the internet has long only had good pages: The growing digitization Also attracts more and more cybergangsterwho wishes to access their sensitive data with the help of security gaps or malware. It is not uncommon for you to use freely accessible software. Here we tell you which legal hacking tools are available and like them Criminals on the Internet so that even a step forward.
- Destructive hackers abuse legal software for illegal purposes.
- Mobile devices are also increasingly becoming the goal of the attackers from the Internet.
- With the help of hacking tools, you can identify and correct the weak points in your network.
1. Five Hacker tool kits, which you legally get on the Internet
Hacking of the software rushes a bad reputation, which does not mean that it is inevitably always illegal. Legally get the following five internet utilities.
1.1. Aircrack uses security gaps in your WLAN
With Aircrack you get immediately Several programs with the help you can explore the weak points in the networks and take advantage of it. The main tool of the instrument kit is the Decrypration Aircrack-NG software, which Discover Wlans security keys protected by Wep and WPA2 Candies. To this end, the so -called breed strength method is used for WEP, which means that all possible numbers and combinations of letters are simply tried.
Aircrack -ng only needs a few seconds to break a WEP key. For more complex WPA2 experts, on the other hand, it falls on dictionary attacks, in which the password is determined on the basis of a password list. However, this method only works WIf the password is made up of a sensitive string.

In addition to Aircrack -ng, the instrument package contains the following sub-programs:
- Airbase -ng With the help of the SSID scans received, it is an access point.
- Airdecap -ng Cracks Wip and WPA data from Wifis with the help of a well -known key.
- Aireplay -ng Networks infiltrated with car packages -Create.
- Airodump -ng Draw data traffic and indicate the information on the network.
- Airolib-nng It manages and saves password and Essid lists for the calculation of WPA keys.
- Airserv-nng Authorized network cards that are not locally connected through a TCP connection.
- AIRTUN-NNG Build virtual tunnels.
1.2. The matrix fits with NMAP
The NMAP network tool is part of the category of so -called doors scanners: eg monitored All doors up to 1024 And also that when they are archived in the program of the program. In addition, of course, there is also the possibility of specifying the dedicated doors for control. However, NMAP only performs scans on target systems if they are be hosted by the user himself Or the operator gave his permission for this.
NMAP is a purely based tool on the text that Originally developed for Linux (GNU) he became. In the meantime there is also one with Zenmap Version of the program with graphic interface. If you have already acquired experience with the input line tools, it should Management on the console, however, no challenge represent them for them. For example, start a simple scan with the command
nmap OR nmap
Using the example Google (www.google.de, 172.217.19.99), the result therefore seems to be this:

Good to know: The Nessus vulnerability scanner also carries out the search for open doors with Nmap.

Nmap va Hollywood: NMAP has also been used for «network analysis» in well -known films:
The «Matrix Reloaded» program has so far had its greatest appearance. Hacker Trinity uses one in the film weakness discovered by the softwarepenetrate the network of an electric power plant. On the contrary, a previous version of Zenmap appears in the success «The Bourne Ultimatum».
1.3. Wireshark cuts network traffic 
The «WireShark» Open Source tool is a network sniffer with which you can use the Cut traffic on any interface And therefore the results can be displayed through the GUI. The software supports 472 different protocolssuch as fiberchanes or IPV6.
With the help of Wireshark it is possible to test encryption or keep track of network problems. Hackers mainly use software Password filter and private data from traffic.
In addition to the graphic version, Wireshark also exists as Tool of control line based on TSHARK textThis has the same range of functions e Registrations in the format TCPDUMP saved. In this way, the results can be easily analyzed using the GUI, if necessary.

On purpose: Until some time ago, Wireshark was mainly Under its old name «Ethereeal» known. After a change of employer by the developer, through which he lost the rights on the name, the software was renamed Wireshark.
1.4. Resources hacker manipulates the management of Windows users
 Resource or reshacker hacker is a free utility of the developer Angus Johnson with which View and modify the components of the EXE files allow.
Resource or reshacker hacker is a free utility of the developer Angus Johnson with which View and modify the components of the EXE files allow.
With the help of the software that manipoli, among other things
- Shortcuts
- Menu
- Dialoghe
- Check
- Labeling
And it can also Change the start logo when the computer starts. Originally like Tool for viewing hidden applications files Thought, hacker of resources has now also become a popular tool for Cybergangster, which in this way Increase viruses and trojans on the unnoticed target systems.
Resource hacker contains a resource compiler for *RC files and a decompress for Exhibition and modification of executable files and resource bookcases. If necessary, it is also possible to create completely new resources files with the tool.

Tipp: Resource hacker is equipped with a graphic surface, but the program also offers many ways to process resources through the command line.
1.5. The recovery of the distributed password breaks almost every password
Elcomsoft’s «distributed password recovery» is in contrast with the hacking tools previously mentioned No freewareFor a price of 599 euros (5 customers), however, you get a particularly powerful tool kit with which authorities, forensic technicians and companies also work.
The software is able to break the passwords of over 300 different types of files. In addition to the Office documents and the PDF files, the Password of Personal security certificates, mailboxes and Windows or Linux Login be determined.
For this purpose, the Forta of the Cova method is used or the determination of the key sentences is determined using lists of defined words. The recovery of distributed password works through patented hardware acceleration technology and linear scalability on a maximum of 10,000 computers Up to 250 times faster than comparable decrystography programs. All GPUs of the Nvidia GeForce series are supported, the AMD models and the core of the integrated integrated graphic processor of the Intel CPU.

A warning: With «distributed password recovery», the main keys can also be broken by password managers such as Keepass, G Data or 1password.
2. Conclusion: legal hacking tools are a double -edged sword
Using hacker software, security experts and administrators can Check the information systems on safety gaps and close them in a targeted waySo to get attackers first.
The availability of these programs will also bring many dangersBecause the possibilities that open often try to be used improperly. You are in a criminal right using legal hacking tools in a gray area. However, sabotage computers or foreign data, According to the current law, there is a crime.
Even hacking tools are not authorized to weigh themselves: in some cases, they can make them punishable by distributing or providing the software.
Basically the following are applied: If you want to test one of the above programs, you should do it exclusively on your home computer and, if possible, do not start the query via the network or internet.
latest posts published

Our complete stabilizer test
The best memory supports for Android and iPhone
Convert and edit audio files

Code publishers: you should know these programming tools
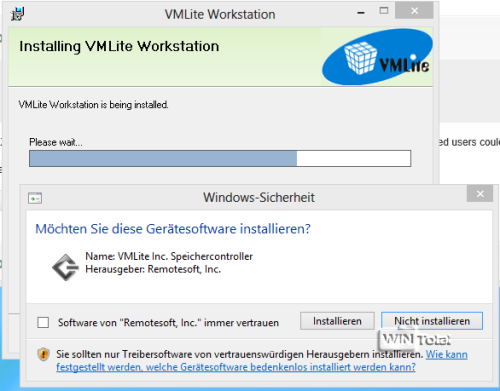
XP mode in Windows 8 with VMLite

How problematic are smartphones for the environment?

Make a period of time with a GoPro: how to do it?

The best round -based strategy games for the PC

Pay to Vince: the monetization of video games



 (27 votes, media: 4.70 out of 5)
(27 votes, media: 4.70 out of 5)