In today’s world, computers, cell phones and internet software have become an integral part of everyday professional life. Corona Pandemic has also presented many challenges in the field of digitization. After data protection becomes more relevant and complex, entrepreneurs are worried about responsibility, if something was wrong. For this reason, there are now so -called IT insurance. This new type of insurance company protects themselves and third parties from fraud on the internet, data losses or other risks. The following overview shows who makes this new insurance coverage.
When is IT insurance needed?
The question whether or not it is useful to computer insurance because a flat rate cannot be answered. Not all digital works must be insured. First of all, it always depends on a decent risk analysis, here you can see quickly What damage can occurHow high the costs would be and if computer insurance would make sense if it does not completely cover your single area. A large group that is based on digitization requires more protection than the master around the corner, which saves its customers in an Excel table.
With a so -called computer risk control, it is possible to quickly determine if the IT insurance is relevant in your case. In this check, you usually answer some simple questions that aim to digitize the company. The more data are archived and digitally processed, the greater the risk and therefore the need for this insurance. Another important parameter of these online checks is the sale of the company.
What protects computer insurance?
Computer insurance covers the damage caused by the insured company and in most cases also those that arise for the company from third parties. This includes almost any type of computer crime.
Examples of damage from third part
Thram are intended as third party damage that affect your customers or other third parties. If you use an EDP system and take place there, it may happen that the attackers can obtain data that are actually confidential. If this illegal dissemination of personal data causes damage, your company is responsible.
Another example would be the simple e-mail if the wrong receiver was inserted. Here too there is an unauthorized publication of personal data (an address and -mail now counts in this category!), Which is mainly covered by cyber insurance.

Examples of self -amazing
On the other hand, there is the car -so called, that is, all the damage that occurs directly to the company. Here too the palette of possible risks is very extensive. Starting from the classic theft of a laptop or a data carrier, on a targeted Hacker attack on the net of the company, up to data protection injuries.
For most companies, this car -ominium is not relevant only for the financial aspect, but also for public reputation. Why who would like to become a customer of a company that does not respond appropriately to these influences?
Computer insurance experts included
In addition to all financial advantages, you should not ignore the most pleasant advantage of IT insurance: many IT insurance providers Team of IT security expertsThat they are not only advisable to help you in an emergency, but also to work on site, for example to prevent an ongoing hacker attack and protect the IT infrastructure. Therefore, it is worth taking a look at the exact services of the individual suppliers and a direct comparison in any case.
Design your insurance protection
It would be measured that IT insurance can always cover all possible dangers, because the digital world is simply too complex and the number of possible risks is too large.
In any case, it is necessary to consider an intensive advice with an expert or directly with the insurance consultant. The insurance benefit must be adapted to your company and your individual needs, otherwise the best computer insurance does not bring you anything, because the insurer can demonstrate compulsory insurance approved through a lack of protective measures in case of damage. Therefore, despite the insurance, you must clean up in the IT department and keep your infrastructure’s safety updated.
latest posts published

Our complete stabilizer test
The best memory supports for Android and iPhone
Convert and edit audio files

Code publishers: you should know these programming tools
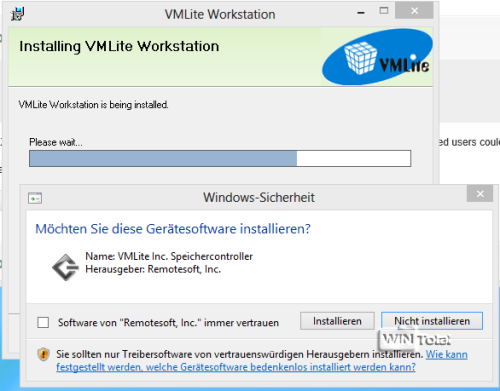
XP mode in Windows 8 with VMLite

How problematic are smartphones for the environment?

Make a period of time with a GoPro: how to do it?

The best round -based strategy games for the PC

Pay to Vince: the monetization of video games




 (30 votes, media: 4.00 out of
(30 votes, media: 4.00 out of